使用如下脚本进行modbus协议代码扫描
import pyshark
def get_code(target_pcap):
captures = pyshark.FileCapture(target_pcap)
func_codes = {}
for c in captures:
for pkt in c:
if pkt.layer_name == "modbus":
func_code = int(pkt.func_code)
if func_code in func_codes:
func_codes[func_code] += 1
else:
func_codes[func_code] = 1
print(func_codes)
if __name__ == '__main__':
target_pcap = "Modbus.pcap"
get_code(target_pcap)发现代码16只有两个包,很异常

使用如下脚本读取代码16的数据
import pyshark
def find_flag(target_pcap, target_code):
cap = pyshark.FileCapture(target_pcap)
idx = 1
for c in cap:
for pkt in c:
if pkt.layer_name == "modbus" and int(pkt.func_code) == target_code:
payload = str(c["TCP"].payload).replace(":", "")
print(hex_to_ascii(payload))
print("{0} *".format(idx))
idx += 1
def hex_to_ascii(payload):
data = payload
flags = []
for d in data:
_ord = ord(d)
if (_ord > 0) and (_ord < 128):
flags.append(chr(_ord))
return ''.join(flags)
if __name__ == '__main__':
target_pcap = "Modbus.pcap"
target_code = 16
find_flag(target_pcap, target_code)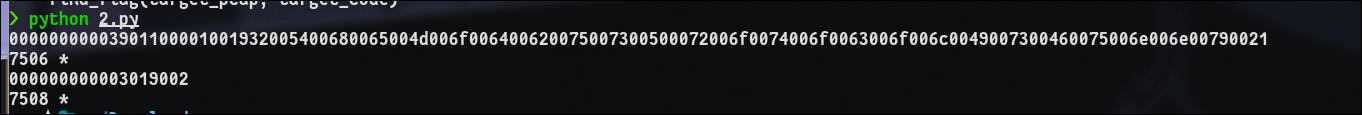
将十六进制转化成字符串获得flag